Unless you’ve been living under a rock and haven’t read any news, social media, or even talked to anyone for the past week and a half, you know that some really screwed up stuff’s been happening. In this article, we’ll touch lightly on what all happened in DC, the fallout, and the reason why Parler was kicked off of AWS. Contrary to the popular “conspiracy theory” belief, we will step through why Parler was kicked.
Comments closedYour Warranty Is Void.com Posts
Anyone that’s been online as long as I have (and yes, there are many that have been online for far longer) knows that your passwords getting leaked and compromised isn’t a question of “if” but rather a question of “when”. As we continue onward in the online world, it’s critically important now more than ever to have a strong password policy and to actually enforce your strong password policy! I italicized the last bit as this will be the crux of this entire article as I experienced a password breach for the first time.
Comments closedThis quick hack is a quick “need to know” list of Linux’s smartctl commands for hard drive diagnosis. I highly recommend using a USB drive…
Comments closedTo set the scene for this quick hack, I needed an MSDOS bootable USB drive so that I could flash firmware for a FreeNAS box…
Comments closedBetween work and life in general, I haven’t had much time to come up with really noteworthy long posts like I’ve been. It’s been several…
Comments closed In this article, I’ll be going over my setup for being able to join my camper’s wireless network to a host wireless network (RV park wifi, state park wifi, etc..) with the purpose of maintaining security and convenience between switching wireless networks. Even though you’re on-the-go, you shouldn’t sacrifice security for convenience of park wifi, and at the same time, changing the wireless configuration on a slew of devices is inconvenient at best and maddening at worst. First I’ll cover why you want to consider this method versus other methods, then I’ll itemize a product list, then finally we’ll jump right into configuration. When we’re done, you’ll have your trusted wireless network all set up and ready for your devices.
In this article, I’ll be going over my setup for being able to join my camper’s wireless network to a host wireless network (RV park wifi, state park wifi, etc..) with the purpose of maintaining security and convenience between switching wireless networks. Even though you’re on-the-go, you shouldn’t sacrifice security for convenience of park wifi, and at the same time, changing the wireless configuration on a slew of devices is inconvenient at best and maddening at worst. First I’ll cover why you want to consider this method versus other methods, then I’ll itemize a product list, then finally we’ll jump right into configuration. When we’re done, you’ll have your trusted wireless network all set up and ready for your devices.
You don’t have to be an elite hacker to keep your personal data personal and in this first part of the two part series discussing Facebook and the Cambridge Analytica scandal, we’ll walk through securing your browser and Facebook all while discovering what exactly Facebook’s been hoarding about us. In the second part of this series, we’ll go over how advertising turned from that annoying clip on TV and Radio to one of the most sinister methods of “Big Data” Matrix-esque surveillance to date.
Comments closed
Good fortune has smiled upon me. My company offered to send me to DEFCON 25, flight and hotel paid. In this article, I’ll talk about DEFCON 25, the sights, the sounds, and my experiences of a hardware geek gone to the world-renowned hacker mecca. If you have ever wanted to go to DEFCON but aren’t quite sure what to expect, I have provided a summary of the trip as well as an important “FNG TIPS” list of things you want to be aware of before you leave.
Comments closed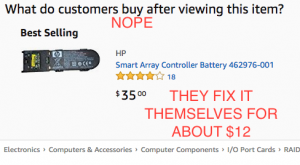
Everyone knows that in most if not all devices, batteries are considered a wear item, an item that’s designed to be replaced at certain intervals of a machine’s lifetime. (Ok, unless you’re Samsung… or Apple… or any one of a bunch of stupid laptop vendors) Enterprise level servers are no exception. What is outrageous though is these consumables are usually stupidly expensive and can be repaired for much less than the replacement part. In this case (and this post), I saved myself about $63 by building my own replacement battery pack for my HP SmartArray P400 raid card.
Comments closed