Hardware
Breathing new life into Ruckus SmartZone 100 controllers (now EOL’d)
by firestorm_v1 on May.02, 2024, under Hardware, Investigative Dissassembly, Networking
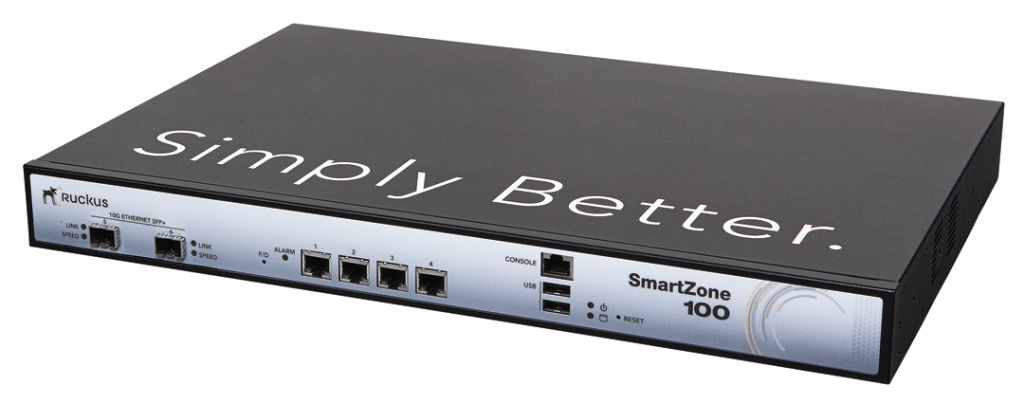
Just like with most things, IT equipment has to evolve over time and wireless connectivity is one of those things. The company I work for decided to replace their aging Ruckus controllers and access points with Meraki access points (The decision was way above my paygrade) so that left a treasure trove of hardware behind that was destined for the waste bin. In this article, I’ll talk about the HA pair of the SmartZone100 controllers from Ruckus, their hardware capabilities, and what I plan on doing with my pair.
(continue reading…)EAS Decoding for fun using the TFT EAS911 ENDEC
by firestorm_v1 on Jul.25, 2023, under Hardware, RF and Radio

The Emergency Alert System (EAS) is a US Nationwide alerting platform that uses a combination of terrestrial radio and television broadcasters to get an urgent message out to as many people as possible. In this article, we’ll be setting up the TFT EAS-911 ENDEC so we can receive these messages without being dependent on cellular service or Internet access.
(continue reading…)Generators and Open Source Part 2 – Always a better mousetrap
by firestorm_v1 on Feb.15, 2022, under Embedded devices, Hardware, Hardware Pr0n, How-To's, Miscellaneous
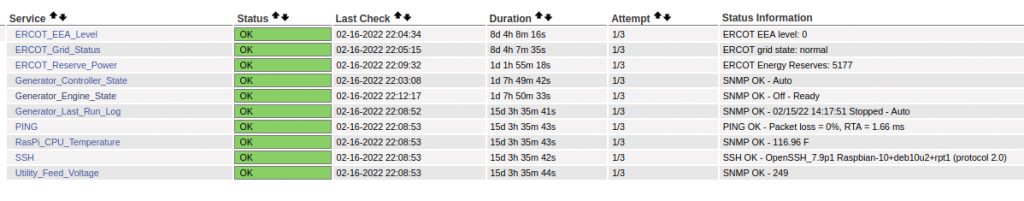
In Part 1, I discussed the research, physical installation, a bit of maintenance, and the overall basic operation of the Generac 22kW Guardian whole home generator. In this post, we’ll go over the monitoring of the generator and quickly outline the vendor’s supplied option as well as the Open Source option I decided on, and even up contributing to! Yes, even though I’m not a developer, I managed to contribute to an Open Source project and helped the developer out!
(continue reading…)Generators and Open Source Part 1 – Learning from the past
by firestorm_v1 on Feb.15, 2022, under Hardware, Hardware Pr0n, Product Reviews

Being a homeowner isn’t for the faint of heart, there’s always a chance for things to go wrong, especially considering that we’re in Texas and well… *gestures at the Valentine’s day week of February 2021*. So with that being said, as soon as the ink was dry on our house contract and we had closed, I was already in process of soliciting for a standby whole home generator. This three part article will cover everything from the decision making process of the generator and its installation (this article), how I monitor the generator using GenMon, an opensource application suite on Github (Part II), and lastly, how I implemented Grafana, Prometheus, and SNMP Exporter (Part III) to get the level of monitoring I am comfortable with.
(continue reading…)Quick Hack: Smartctl tests in a nutshell
by firestorm_v1 on Nov.19, 2019, under Hardware, Miscellaneous, Quick Hacks
This quick hack is a quick “need to know” list of Linux’s smartctl commands for hard drive diagnosis. I highly recommend using a USB drive dock for analyzing suspect drives. These commands are OS agnostic provided you’re running the vendor provided smartctl for either Linux or BSD.
For the purposes of this article, /dev/sdb is the drive under test. Make sure you know which /dev entry corresponds with the desired drive.
smartctl -a /dev/sdb Shows all smart attributes of /dev/sdb including test results, and drive make, model, and serial number.
smartctl -t short /dev/sdb Performs a “short” online test of /dev/sdb. Does not print test results. Does not test disk surface readability.
smartctl -t long /dev/sdb Performs a “long” offline test of /dev/sdb. Does not print test results. Tests the entire disk surface for readability and reallocates bad sectors. If your system is under a lot of disk I/O to the disk under test, this will cause the test to take longer to complete (hence running it in a USB dock or other non-system location)
smartctl -c /dev/sdb Estimates how long the disk check will take in minutes (Usually is wrong though, I wouldn’t set my watch by it.)
smartctl -l selftest /dev/sdb Shows the SMART test results table (instead of smartctl -a which shows EVERYTHING).
smartctl -X /dev/sdb Cancels a test in progress.
NOTES: Re-running smartctl -t against a drive already testing will show an error message which includes how long the test will take to complete (unlike smartctl -l, this time is actually more closer to reality).
In some installations that support it, hdparm -S 0 /dev/sdb will prevent a disk from going to sleep, however in theory, the disk should never sleep if it’s under an active test. This will not stop an ACPI sleep or hibernate event from shutting down the disk.
Happy hacking!
FIRESTORM_v1
Cruising with WiFi – Is that a travel router in your pocket?
by firestorm_v1 on Jan.10, 2019, under Embedded devices, Hardware, Networking

Carnival Vista
Internet access on cruise ships is now a common occurrence and more commonly, I get frequent questions on how to “game” the system and get Internet access without paying for it. The short of it is, you’re going to have to purchase at least one account to get anything online. The long of it lies in the rest of this article and it’ll be up to you to decide if it’s worth the effort. Quick spoiler alert: For me it wasn’t, and I ended up buying another access to get myself and my wife online at the same time. While it was a punch in the pocketbook, it was a lot cheaper to pay money to resolve than the costs incurred in other areas (time, frustration, etc.).
Networking on the Go – Creating a trusted wireless network in a sea of untrusted wireless
by firestorm_v1 on Aug.18, 2018, under Hardware, Networking, Security
 In this article, I’ll be going over my setup for being able to join my camper’s wireless network to a host wireless network (RV park wifi, state park wifi, etc..) with the purpose of maintaining security and convenience between switching wireless networks. Even though you’re on-the-go, you shouldn’t sacrifice security for convenience of park wifi, and at the same time, changing the wireless configuration on a slew of devices is inconvenient at best and maddening at worst. First I’ll cover why you want to consider this method versus other methods, then I’ll itemize a product list, then finally we’ll jump right into configuration. When we’re done, you’ll have your trusted wireless network all set up and ready for your devices.
In this article, I’ll be going over my setup for being able to join my camper’s wireless network to a host wireless network (RV park wifi, state park wifi, etc..) with the purpose of maintaining security and convenience between switching wireless networks. Even though you’re on-the-go, you shouldn’t sacrifice security for convenience of park wifi, and at the same time, changing the wireless configuration on a slew of devices is inconvenient at best and maddening at worst. First I’ll cover why you want to consider this method versus other methods, then I’ll itemize a product list, then finally we’ll jump right into configuration. When we’re done, you’ll have your trusted wireless network all set up and ready for your devices.
Overhauling the Battery Backup in an HP DL380
by firestorm_v1 on Jun.20, 2017, under Hardware, How-To's
Everyone knows that in most if not all devices, batteries are considered a wear item, an item that’s designed to be replaced at certain intervals of a machine’s lifetime. (Ok, unless you’re Samsung… or Apple… or any one of a bunch of stupid laptop vendors) Enterprise level servers are no exception. What is outrageous though is these consumables are usually stupidly expensive and can be repaired for much less than the replacement part. In this case (and this post), I saved myself about $63 by building my own replacement battery pack for my HP SmartArray P400 raid card.
Home Automation – Making a dumb switch for smart lights.
by firestorm_v1 on Feb.23, 2016, under Embedded devices, Hardware, How-To's, IoT
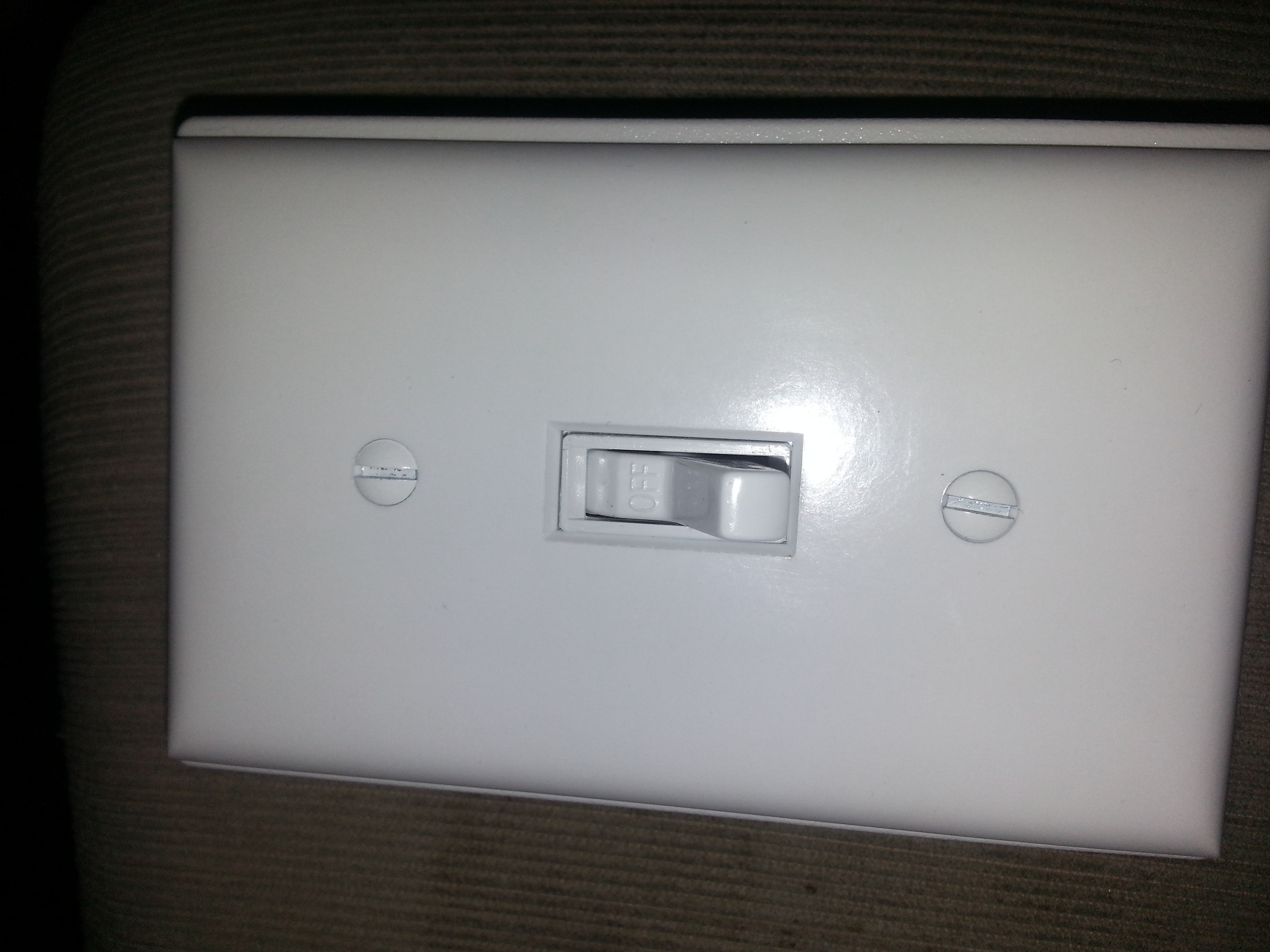 It might not look like much, but the switch used as this feature image has more to offer than one would think judging by appearances. In this article, we will be converting a “stupid” switch into a “smart” switch for the purposes of controlling a connected GE Light Bulb over Z-wave and discuss why you’d want to look for a stupid switch for smart devices in the first place. (continue reading…)
It might not look like much, but the switch used as this feature image has more to offer than one would think judging by appearances. In this article, we will be converting a “stupid” switch into a “smart” switch for the purposes of controlling a connected GE Light Bulb over Z-wave and discuss why you’d want to look for a stupid switch for smart devices in the first place. (continue reading…)
Cisco WiFi – Disconnect from the hive mind
by firestorm_v1 on Jul.16, 2015, under Embedded devices, Hardware, How-To's, Linux, Networking

Cisco AIR-AP1131AG-A-K9
Everyone knows that I love a bargain. That love for bargains is intensified any time networking gear is involved. Imagine my excitement when I found a bunch of the above pictured Cisco access points on Ebay for around $8 a pop because the lid won’t stay on. Unfortunately, my excitement was tempered a bit when I found out that these were designed to work with a controller and weren’t stand alone units. Undeterred by this disappointment, I researched and found a way to get these things to operate on their own as standalone units and freed them from the hive mind! In this article, we will cover converting the Cisco AIR-AP1131AG-A-K9 from “Lightweight”(controller-based) to “Autonomous”(standalone) and will even cover how to put them back in “Lightweight” mode if you want later on.