Linux
Unifi Video NVR – Gone… and back again!
by firestorm_v1 on Oct.24, 2024, under Embedded devices, Hardware, Hardware Pr0n, Investigative Dissassembly, Linux, Miscellaneous

Over the weekend, I was digging through the expansive parts bin known as the computer room and I had my old Unifi Video NVR jump off the shelf at me. While the Unifi Video product has long since been discontinued, giving way to the Unifi Protect line of NVRs and products, the hardware itself still has a bit of life left to it. In this article, I’ll go over the hardware of the derelict product and see what we can do with it going forward.
(continue reading…)How to use Nagios and NRPE to monitor remote OPNSense HA secondary routers
by firestorm_v1 on Jul.19, 2024, under Linux, Networking, Software
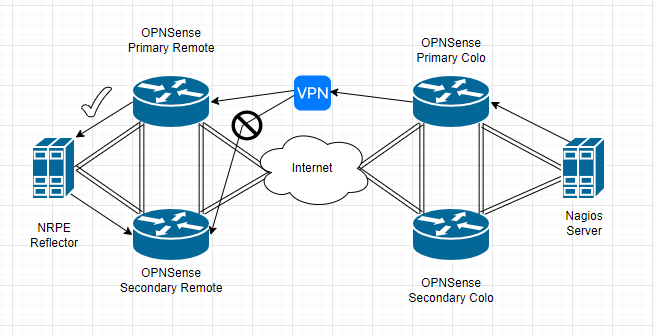
In this article, I’ll be discussing how to use the Nagios NRPE (Nagios Remote Program Executor) service to monitor the remote secondary OPNSense firewall in a high availability configuration to overcome a VPN routing limitation where the secondary instance is not reachable. The root cause is due to the way the VPN routing is performed in OPNSense where the incoming traffic flow won’t communicate due to a routing conflict. While this issue isn’t an OPNSense specific issue (it affects pfSense and other firewalls that use HA/CARP with VPN).
(continue reading…)Cisco WiFi – Disconnect from the hive mind
by firestorm_v1 on Jul.16, 2015, under Embedded devices, Hardware, How-To's, Linux, Networking

Cisco AIR-AP1131AG-A-K9
Everyone knows that I love a bargain. That love for bargains is intensified any time networking gear is involved. Imagine my excitement when I found a bunch of the above pictured Cisco access points on Ebay for around $8 a pop because the lid won’t stay on. Unfortunately, my excitement was tempered a bit when I found out that these were designed to work with a controller and weren’t stand alone units. Undeterred by this disappointment, I researched and found a way to get these things to operate on their own as standalone units and freed them from the hive mind! In this article, we will cover converting the Cisco AIR-AP1131AG-A-K9 from “Lightweight”(controller-based) to “Autonomous”(standalone) and will even cover how to put them back in “Lightweight” mode if you want later on.
Raspberry Pi tastes better with RPi B+ edition
by firestorm_v1 on Jul.23, 2014, under Embedded devices, Hardware, Hardware Pr0n, Linux
The Raspberry Pi Foundation announced a new arrival to their existing line of awesome little credit-card sized computers. I was fortunate enough to get my hands on one and give it a go. In the article (with pics!) below, I’ll cover what’s changed, what’s stayed the same, and what you can expect from everyone’s favorite mini machine.
How to build a [better] Minecraft Server
by firestorm_v1 on Mar.10, 2013, under How-To's, Linux, Toys and Games

Quite some time ago, I posted an article on how to build a basic Minecraft Server which served to get you up and off the ground with multiplayer gameplay. It’s been two years since that article was posted and there have been so many advances in the Minecraft Server realm from administration changes (now you have a fancy GUI) to core game changes that allow for the modification for just about everything gameplay related. Popular alternative servers (Bukkit, Tekkit, Feed The Beast, etc..) allow for mods to be used which can drastically expand your Minecraft experience. This howto will detail the process going from a basic Debian server installation to a fully fledged vanilla Minecraft server with a browseable map. Read on for the full article, it’s pretty long but we have a lot to cover. (continue reading…)
CVS Netbook Revisited
by firestorm_v1 on Jul.25, 2011, under Embedded devices, Hardware, How-To's, Linux, Software

A few months ago, I posted a hardware teardown of the CVS Sylvania Netbook pictured above. After working with it and performing a lot of research on it, I promised a follow up article, and here it is. To sum it all up, with a bit of modification to the software, a spare SD card and a lot of patience, you can actually turn this thing into a somewhat useful Linux device. There’s also some improvements and suggestions to be had for improving the Windows CE side of things should you decide to continue using it in its default state.
Building Snort and Nessus – Ubuntu IDS Part 3
by firestorm_v1 on May.20, 2011, under Hardware, How-To's, Linux, Security, Software
 In this final article in the three part Ubuntu IDS series, we will go over installing, compiling and configuring Snort and Nessus on our new IDS device. We will use Snort to analyze traffic as seen by the IDS and we will use Nessus to perform vulnerability testing on the network. The process for installing Snort will also cover installing SnortReport provided by Symmetrix Technologies so we can translate Snort’s cryptic messages into a more readable format that we can take action on. Read on as we wrap up the installation and finish our IDS device.
In this final article in the three part Ubuntu IDS series, we will go over installing, compiling and configuring Snort and Nessus on our new IDS device. We will use Snort to analyze traffic as seen by the IDS and we will use Nessus to perform vulnerability testing on the network. The process for installing Snort will also cover installing SnortReport provided by Symmetrix Technologies so we can translate Snort’s cryptic messages into a more readable format that we can take action on. Read on as we wrap up the installation and finish our IDS device.
Setting up bonding networking -Ubuntu IDS Part 2
by firestorm_v1 on May.04, 2011, under Hardware, How-To's, Linux, Security, Software
In an earlier article, I demonstrated how you can build a passive monitoring device for an Ethernet network as the first part to a three part project to build a home IDS device. In this article, the second in the series, I will describe how to set up the networking for an IDS using the passive tap that I built earlier.This setup will involve using a technique called bonding to take two physical interfaces and bond them together, creating a logical interface that we can use for Snort. This article will also explain where is the best location to place the tap and what you can expect to see once the networking is set up using common Linux utilities like tcpdump.
Build a Passive Ethernet Tap – Ubuntu IDS Part 1
by firestorm_v1 on Apr.06, 2011, under Hardware, How-To's, Linux, Security, Software
One of the things that the GCIA study has taught me is that being able to monitor the network your computer is on is a critical necessity to maintaining a secure network. Corporate environments can set up IDS devices to monitor traffic however monitoring doesn’t work unless you have proper connectivity to what you want to monitor. Unfortunately, most of us don’t have central wiring in our house and expensive managed switches that can set up span sessions with which to monitor traffic in transit. In this HOWTO, I will cover how to build your own monitoring connection that you can use on your own network to monitor traffic without breaking the bank. This article is first in a three part series on how to build your own home IDS for monitoring your network traffic. Look for the other two sections soon!
(continue reading…)
Installing Minecraft Server in Ubuntu Server
by firestorm_v1 on Jan.09, 2011, under How-To's, Linux, Software
 Ok, I’ll admit it. I’ve been caught by the Minecraft bug. It bit me hard and of course I learned rather quickly that there is a problem with using two laptops to play Minecraft on and that is that it’s a pain in the posterior to move your save games around. In this article, I will be covering how to install Minecraft Server on a new installation of Ubuntu 9.04LTS. These instructions will work for all current versions of Ubuntu, so if you’re using something newer or something older, these instructions should get you up and running in no time. (continue reading…)
Ok, I’ll admit it. I’ve been caught by the Minecraft bug. It bit me hard and of course I learned rather quickly that there is a problem with using two laptops to play Minecraft on and that is that it’s a pain in the posterior to move your save games around. In this article, I will be covering how to install Minecraft Server on a new installation of Ubuntu 9.04LTS. These instructions will work for all current versions of Ubuntu, so if you’re using something newer or something older, these instructions should get you up and running in no time. (continue reading…)


